In the evolving landscape of Cosmos interchain security, validators face unique challenges and opportunities when leveraging the Inter-Blockchain Communication (IBC) protocol. Interchain Security (ICS) empowers provider chains like the Cosmos Hub to extend their proof-of-stake security to consumer chains, allowing validators to secure multiple sovereign networks without diluting their core commitments. This shared security model, built atop IBC, promises efficiency but demands rigorous discipline. As a validator, embracing cosmos interchain security best practices is not optional; it is essential for safeguarding stakes and optimizing rewards in a multi-chain ecosystem. This IBC validator guide outlines six prioritized strategies tailored for Cosmos SDK security in IBC environments, drawing from real-world deployments and protocol insights.
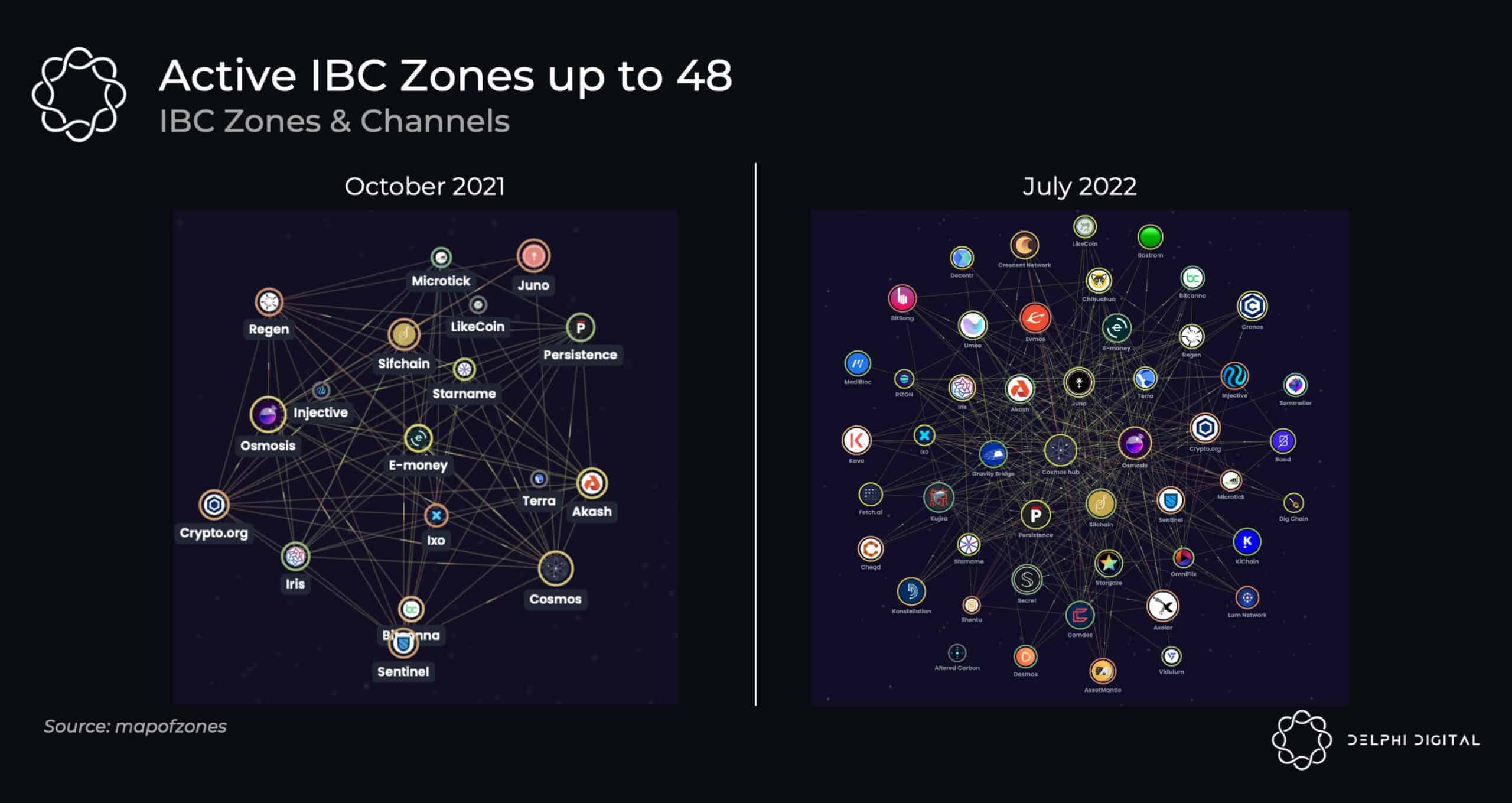
Validators who treat ICS as a mere extension of single-chain operations risk correlated failures that could slash yields across portfolios. Conservative approaches, rooted in sovereignty's stability, prioritize risk isolation and proactive oversight. Consider the mechanics: consumer chains rely on provider validators to run dedicated nodes, relay packets via IBC, and enforce consensus. Missteps here amplify vulnerabilities, from double-signing to downtime. By methodically addressing these, validators can harness ICS for enduring value.
Conduct Thorough Due Diligence on Consumer Chains Before Opting In
Opting into a consumer chain is akin to investing in an unproven asset; haste invites regret. Before committing resources, scrutinize the chain's governance history, token economics, and validator incentives. Review on-chain proposals, audit reports, and community sentiment to gauge long-term viability. Weak governance often signals future forks or attacks, exposing your stake to unnecessary peril. In my view, limit opt-ins to chains with proven IBC channel stability and diversified validator sets. This due diligence, while time-intensive, prevents entanglement in failing projects and preserves capital for high-conviction opportunities. Tools like Cosmos explorers and ICS dashboards reveal opt-in statuses; use them to simulate slashing exposure pre-commitment.
Deploy Real-Time Multi-Chain Monitoring with Slashing Alerts
Vigilance defines successful validators in IBC ecosystems. Deploy monitoring suites that track uptime, voting power, and infraction risks across provider and consumer chains simultaneously. Integrate slashing alerts via tools like Prometheus or custom scripts querying IBC packets for validator obligations. Real-time notifications enable swift remediation, such as restarting nodes before jailing thresholds. I advocate for automated dashboards displaying cross-chain health metrics; they transform reactive firefighting into proactive stability. In cosmos interchain security, a single unmonitored downtime event on a consumer chain can propagate slashing to the provider, eroding rewards. Prioritize open-source solutions compatible with Cosmos SDK for seamless integration.
Run Isolated Nodes for Provider and Consumer Chains
Isolation is the cornerstone of robust validator IBC best practices. Never run consumer chain nodes on the same infrastructure as your provider setup; this compartmentalizes failures. Use distinct servers, consensus keys, and network configurations to thwart lateral attacks or software bugs spilling over via IBC relayers. For instance, assign unique keys registered on the provider chain, ensuring infractions remain chain-specific. This approach mirrors portfolio diversification in traditional finance, limiting blast radius. Validators ignoring isolation court systemic risks, especially as consumer chains mature and attract sophisticated adversaries. Invest in containerized environments like Docker or Kubernetes for scalable, auditable deployments.
These initial strategies lay a firm foundation, mitigating the most pervasive threats in cosmos SDK security IBC operations. Yet true mastery requires extending this discipline further.



No comments yet. Be the first to share your thoughts!